Introduction: The Growing Threat of Email Account Hacks
In today’s digital-first world, email accounts are no longer just communication tools—they are the backbone of personal and professional identity. From banking credentials and social media access to business communications and sensitive documents, a single email account often serves as the gateway to an individual’s entire digital ecosystem.
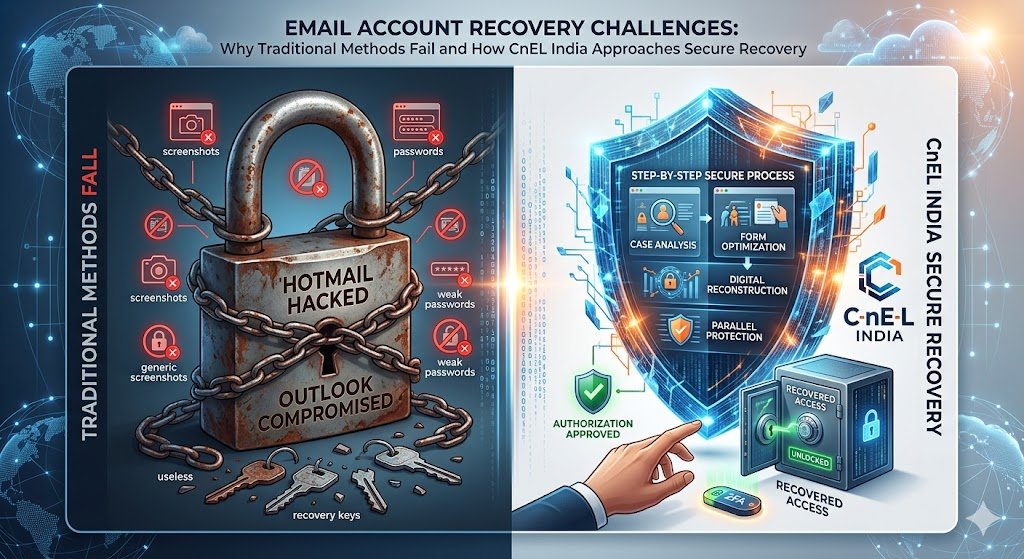
Unfortunately, this centralization has made email accounts one of the most targeted assets for cybercriminals. Cases of hacked email accounts—especially long-standing accounts like Hotmail or Outlook—are increasing rapidly. Victims often find themselves locked out, while attackers exploit the compromised account to gain access to other platforms.
At CnEL India, we frequently encounter users who have exhausted all automated recovery options but still fail to regain access. This highlights a major gap between user expectations and the reality of automated security systems.
Understanding the Problem: Why Email Recovery Is So Difficult
Most major email providers rely heavily on automated recovery systems. These systems are designed with one primary goal: security over convenience. While this approach protects users from unauthorized access, it also creates significant challenges for legitimate account owners.
1. Automated Recovery Systems Have Limitations
Recovery systems depend on data verification such as:
- Previous passwords
- Frequently contacted email addresses
- Subject lines of past emails
- Account usage patterns
However, if a hacker has already altered account activity or recovery details, the system may no longer recognize the original owner.
2. Long-Term Accounts Are More Vulnerable
Accounts that have been used for 10–20 years often:
- Have outdated recovery information
- Lack updated security settings
- Are linked to multiple third-party services
This makes both hacking and recovery more complex.
3. Lack of Human Support
One of the biggest frustrations users face is the inability to connect with a real support agent. Most platforms prioritize automated assistance, leaving users stuck in repetitive recovery loops.
Real-World Impact of a Hacked Email Account
The consequences of losing access to an email account can be severe and far-reaching:
1. Financial Risks
Hackers may attempt to access:
- Banking accounts
- Payment platforms
- Investment accounts
2. Identity Theft
Personal data stored in emails can be used to:
- Impersonate the user
- Commit fraud
- Access confidential services
3. Business Disruption
For professionals and business owners:
- Client communication is interrupted
- Important contracts and data may be lost
- Brand reputation can be damaged
4. Emotional and Psychological Stress
Losing access to years of personal data, conversations, and memories can be extremely distressing.
Common Mistakes Users Make During Recovery
At CnEL India, we have observed several recurring mistakes that reduce the chances of successful recovery:
1. Submitting Incomplete Information
Users often provide generic or vague answers instead of precise details.
2. Repeated Failed Attempts
Submitting the same incorrect or weak information multiple times can reduce the system’s trust score.
3. Relying on Screenshots as Proof
Most recovery systems do not consider screenshots as valid ownership proof.
4. Ignoring Linked Account Security
Many users focus only on the hacked email while ignoring other compromised accounts.
CnEL India’s Approach to Email Account Recovery
While no third party can bypass official systems, a structured and strategic approach can significantly improve recovery success rates. At CnEL India, we focus on guidance, preparation, and digital security strengthening.
1. Case Analysis and Assessment
We begin by understanding:
- The timeline of the hack
- Changes made by the attacker
- Recovery attempts already made
This helps in identifying gaps in previous recovery submissions.
2. Recovery Form Optimization
Instead of random attempts, we guide users to submit high-quality recovery requests by including:
- Accurate historical passwords
- Specific email subject lines
- Frequently contacted recipients
- Account usage patterns
The goal is to align the response with how automated systems validate ownership.
3. Digital Footprint Reconstruction
We help users reconstruct their digital activity by:
- Reviewing old devices
- Checking saved credentials
- Identifying linked platforms
This improves the depth and accuracy of recovery information.
4. Parallel Account Protection
While recovery is ongoing, we ensure:
- All linked accounts are secured
- Passwords are updated
- Two-factor authentication is enabled
This prevents further damage.
5. Professional Communication Support
In cases where support channels are available, we assist users in:
- Drafting clear and effective support requests
- Communicating technical issues properly
- Escalating the issue when possible

Why “Quick Fix” Solutions Are Dangerous
Many users, out of desperation, turn to unauthorized recovery services. This is extremely risky.
Risks Include:
- Data theft
- Financial scams
- Permanent account loss
- Legal complications
At CnEL India, we strongly advise against:
- Hiring “ethical hackers” for recovery
- Paying for unauthorized access
- Sharing sensitive personal information
Preventive Measures: Securing Your Email Account
Prevention is always better than recovery. Here are essential steps every user should follow:
1. Enable Two-Factor Authentication (2FA)
Adds an extra layer of security beyond passwords.
2. Keep Recovery Information Updated
Ensure your:
- Phone number
- Alternate email
- Security questions
are always current.
3. Use Strong and Unique Passwords
Avoid:
- Reusing passwords across platforms
- Simple or predictable combinations
4. Monitor Account Activity
Regularly check:
- Login history
- Security alerts
- Unknown devices
5. Avoid Phishing Attacks
Be cautious of:
- Suspicious emails
- Unknown links
- Fake login pages
What If Recovery Fails?
In some cases, despite best efforts, account recovery may not be possible. This can happen if:
- The account has been heavily altered
- Recovery data is completely outdated
- Security systems flag the account as high-risk
Next Steps Include:
- Creating a new secure email account
- Recovering linked services individually
- Informing contacts about the compromised account
- Updating login details across platforms
The Role of CnEL India in Digital Security
CnEL India is not just focused on solving problems—we aim to educate and empower users in managing their digital presence securely.
Our Key Focus Areas:
- Digital security awareness
- Data protection strategies
- Account recovery guidance
- AI-based solutions for automation and monitoring
We believe that with the right approach, users can significantly reduce risks and improve their chances of recovery.
Conclusion: A Strategic Approach Is the Only Way Forward
Email account recovery is no longer a simple process. With increasing cyber threats and stricter security protocols, users must adopt a strategic and informed approach.
While automated systems may seem frustrating, they are designed to protect user data. The key lies in understanding how these systems work and aligning recovery efforts accordingly.
At CnEL India, we bridge the gap between users and complex digital systems by providing structured guidance, practical solutions, and a security-first mindset.
If you or your clients are facing similar challenges, remember:
- Avoid shortcuts
- Focus on accurate information
- Strengthen overall digital security
Because in today’s world, your email account is not just an inbox—it is your digital identity.